Identify Image Manipulation
Identify Image Manipulation
KGL’s Image Forensics solution takes the guesswork out of image integrity by evaluating images for suspect manipulation. The process uses specialized image analysis techniques to detect image manipulation or duplication in supplied grayscale or color halftone images.
Keeping It Real
Our graphics and image forensics specialists preflight and analyze all eligible images submitted with a manuscript and generate a report that identifies and explains any suspect or obvious image manipulation. The report is then sent immediately to the publisher for their staff to evaluate the results and then follow their established integrity protocols. The reports are presented as a PDF with “before” and “after” images, including a magnified image of the suspect area. We also use red zones to identify the suspect areas and insert descriptions to explain the items in question. Links to the high-resolution images are provided to the publisher for more in-depth review purposes.
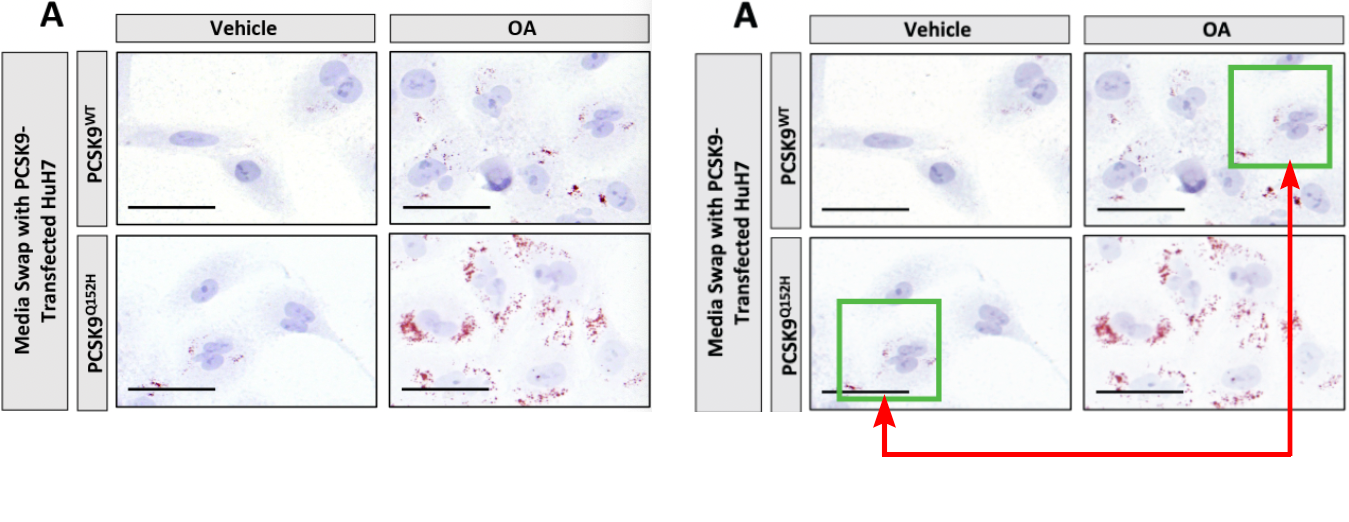
KGL’s methods for performing image forensics on submitted images have been refined from almost 20 years of experience in this field of analysis. Our current techniques include a combination of carefully chosen software-based solutions, like ImageTwin for image duplication detection, and a series of advanced visual checks by highly trained graphics specialists to flag other suspect manipulation.
We continue to research and add software-based solutions to our process as the explosive growth of AI generative tools introduces new challenges for the image forensics service. Publishers can trust that KGL’s image forensics experts are working to stay ahead of the curve when it comes to image integrity and helping to protect the business and reputation of our clients.
Latest Insights
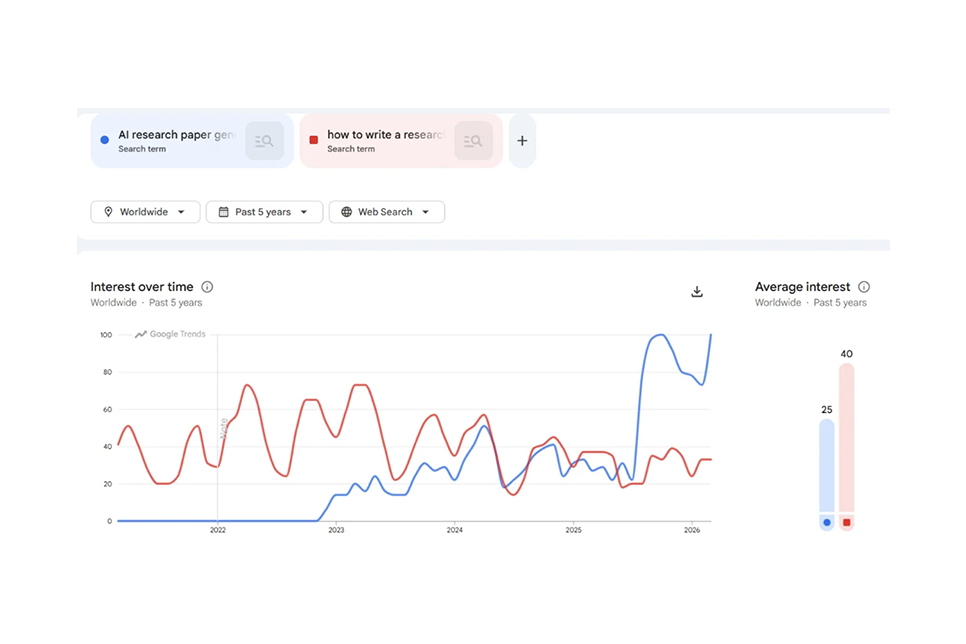
In this blog, KGL Accucoms discusses how researchers are increasingly searching for AI tools to speed up academic writing.
Hong Zhou explores how learning platforms are shifting from delivering content to driving measurable outcomes—powered by AI, trust, and real-world application.
KGL Accucoms VP Simon Boisseau on navigating open access, AI licensing, and why local expertise and human relationships remain the industry's most valuable asset.